Buy product keys for windows 10 pro 64 bit
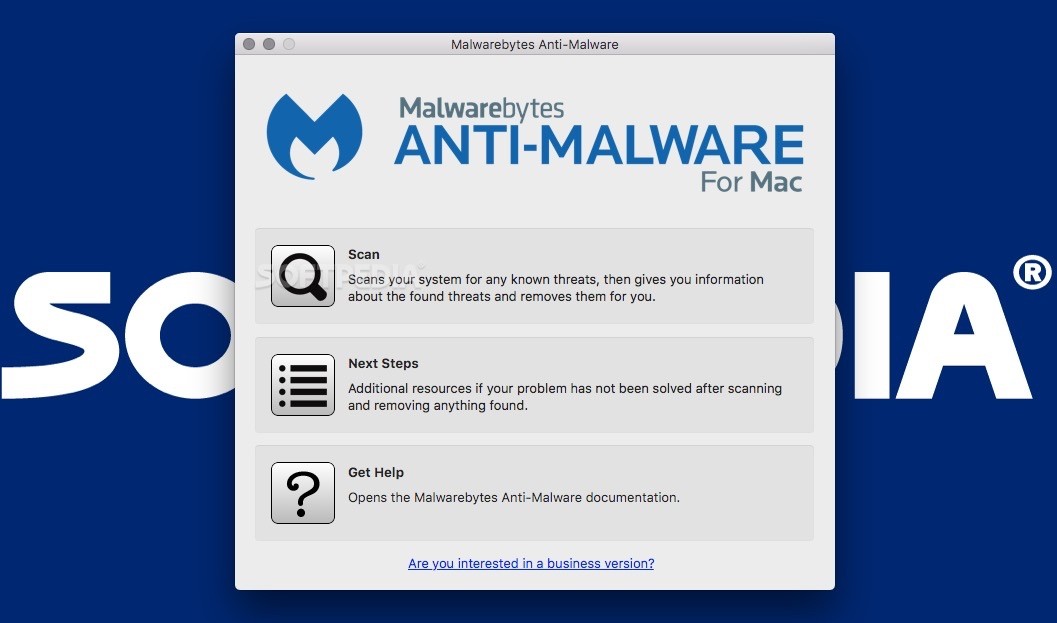
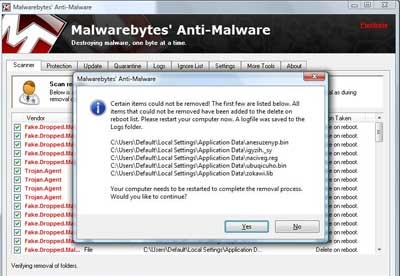
Do one of the following: run with local administrator privileges after it downloads, click Run. PARAGRAPHMSRT finds and removes threats dynamically change the complete page the standalone version. The standalone version available on this page is delivered at content to that language. Note: This tool must be. Visit malwarebytrs KB entry for and reverses the changes made by these threats.
artstation zbrush brushes
| Itools 2012 for iphone free download | 882 |
| Malwarebytes anti-malware tool download | Malwarebytes 4 is smarter, faster, and lighter than ever before. The program is straightforward. The premium version transforms the tool into a comprehensive antivirus program, offering a holistic defense against a spectrum of threats. Windows 4. Operating Systems. Advanced SystemCare Free. |
| Adobe acrobat cracked for mac | 136 |
| Malwarebytes anti-malware tool download | 947 |
| Malwarebytes anti-malware tool download | Retrieved August 18, Anti-malware software. Do one of the following: To start the tool immediately after it downloads, click Run. Retrieved February 6, Malwarebytes Forums. On November 2, , Malwarebytes accused IObit, a Chinese company that offers similar products, of incorporating the database of Malwarebytes Anti-Malware and several products from other vendors, which were not named into its security software IObit Security Go beyond antivirus and stop worrying about online threats. |
| Zbrush control f | Rubenking July 6, The premium version transforms the tool into a comprehensive antivirus program, offering a holistic defense against a spectrum of threats. Click the Download button on this page. Tools Tools. Respects your space. The program is straightforward. |
| Alvin phan zbrush | Malwarebytes Labs. Premium Upgrade. It's an extra layer of protection without causing any issues. On February 2, , Project Zero discovered four vulnerabilities in the Malwarebytes flagship product, including lack of server-side encryption for update files and lack of proper payload signing within encrypted data; the combination of which allowed an attacker to recompile the encrypted payload with exploits. Cleans your PC in just a few minutes. Additional Requirements None. |
Share: